I often talk about converged, multi-model databases from the perspective of developer productivity.
Owning one platform that handles many data types like relational, JSON, graph, vector yields fewer moving parts when building and operating apps.
Recently, another reason is more and more compelling: security.
AI-assisted vulnerability discovery is moving incredibly fast. Anthropic’s Project Glasswing describes frontier models finding and exploiting software vulnerabilities at a level that used to require highly skilled humans. Additionally, the incidence of supply-chain attacks is rising rapidly, and serious bugs like Copy Fail are being surfaced by LLMs.
As advances in AI are make it cheaper to inspect code, reverse binaries, and exploit systems, a question is raised that I think converged data platforms can help answer: How many independently exploitable systems do we want to operate?
Attack Surface
OWASP’s Attack Surface Analysis Cheat Sheet frames attack surface as where data and commands enter and leave a system, the code protecting those paths, and the valuable data being protected. By definition, each new component adds more paths to secure and more code to trust.
You can keep your primary database patched and still carry risk through the whole mess of systems and clients that connect to it.
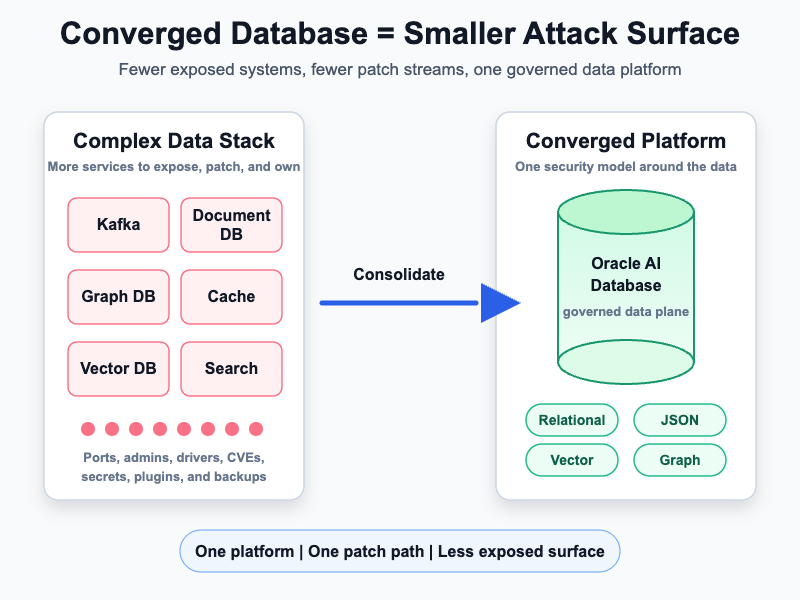
When you add five specialized data components, you don’t just gain their feature set: You add five patch streams, five control planes, five dependency graphs, five backup stories, and five points that are potentially exploitable.
Higher stakes with binary-analysis
Quesma’s BinaryAudit benchmark tested AI agents on backdoor detection in compiled binaries using reverse-engineering tools such as Ghidra and Radare2. The results were mixed, and the authors were clear that the approach is not production-ready. But the useful signal is this: current models can already make progress on stripped executables without source code or debug symbols.
As these tools improve, the long tail of infrastructure becomes more exposed: old connectors, embedded admin services, neglected exporters, vendor appliances, supply chain risks, and database extensions that no one reviewed.
Converged features are security features
Oracle AI Database is an example of how feature consolidation can be a security angle:
A converged database platform for all your data means that your workloads don’t need a separate data platform by default.
For example:
- JSON and document-style workloads can use native JSON support, including transactions, indexing, declarative querying, and views.
- Vector search can use Oracle AI Vector Search, keeping embeddings closer to business data instead of moving them into a separate vector store by default.
- Graph workloads can use native property graph support and query relationships alongside JSON, spatial, and transactional data.
- Some event-driven and microservice patterns can use Transactional Event Queues with Kafka APIs, avoiding a separate streaming platform for cases that do not need one.
Each of these capabilities can replace components you’d otherwise need to patch, monitor, back up, audit, and explain during an incident.
Data platform consolidation is not only simpler, it can reduce attack surface. One platform means fewer privileged administrators, fewer network boundaries, fewer secrets, fewer client libraries, fewer backup surfaces, fewer control planes, and one primary vendor patch stream to track.
Consolidate first, specialize deliberately
I still believe specialized systems have a valuable place, but come with stricter security tradeoffs. Each component needs to earn its place, and architecture decisions made for developer convenience now have a sharper security consequence.
Before adding something new to your stack, ask:
- Am I comfortable accepting the supply chain risk of this product?
- Who patches it, and how quickly?
- Who owns the CVE response?
- Which ports and admin APIs are exposed?
- Which identities can administer it?
- Which client libraries enter application builds?
- Which container images, plugins, and extensions does it depend on?
- Which backups, logs, dashboards, and exporters contain sensitive data?
- What happens when an AI-assisted researcher finds a bug in one of those layers?
Converged database design is a practical way to make the target smaller, keep ownership clearer, and put more security controls around the data that matters. In the AI-assisted threat landscape, feature consolidation is attack-surface reduction.
Leave a Reply